
REVIEW – Internet security is no joke. With increasing data breaches and phishing scams, it’s not uncommon for someone besides you to get ahold of your online account credentials, no matter how safe you’ve been. Adding an extra layer of authentication with a security key, like the YubiKey 5Ci, goes a long way toward keeping your accounts safe.
What is it?
The YubiKey 5Ci is a dual connector (Lightning and USB-C) security key meant to act as a unified security solution across both desktop and mobile devices. It can be used as a secure login key or set up for quick two-factor authentication (2FA).

What’s in the box?
- one YubiKey 5Ci
Hardware specs
- USB Type: USB-C and Lightning
- NFC-enabled: No
- Authentication Methods: Passwordless, Strong Two Factor, Strong Multi-Factor
- Design & Durability: No Batteries Required, No Moving Parts
- Function: WebAuthn, FIDO2 CTAP1, FIDO2 CTAP2, Universal 2nd Factor (U2F), Smart card (PIV-compatible), Yubico OTP, OATH – HOTP (Event), OATH – TOTP (Time), Open PGP, Secure Static Password
- Certifications: FIDO 2 Certified, FIDO Universal 2nd Factor (U2F) Certified
- Cryptographic Specifications: RSA 2048, RSA 4096 (PGP), ECC p256, ECC p384
- Device Type: FIDO HID Device, CCID Smart Card, HID Keyboard
Design and features
I feel like before getting into the review of this specific YubiKey 5Ci, I should write a little explainer of what a 2FA security key is used for.
What the heck is 2FA, anyway?
You might be asking yourself what this two-fah thing is. 2FA, short for two-factor authentication, is an extra layer of security for logging into an account on an untrusted device or computer. Typically this comes in the form of inputting a code sent to a cell phone or, if you have an Authenticator set up with that account, typing in the code from that application. Basically, in addition to your login and password, the second form of authentication is generated on a device that only you can access and not a potential hacker.
With an authentication key, the second authorization factor is a small physical device that you can plug into a USB or Lightning port, or by holding your NFC enabled smartphone close to the key. So rather than having to type in or paste a code from a text or authentication app, plugging in the key and activating it does this step for you. In many cases, it’s faster than accessing the text message or app, and is much more secure.
Setup
The initial setup is, by far, the most time-consuming aspect of owning a security key. The good news is that the number of services that utilize YubiKeys is vast and growing. Services such as password managers, cloud storage, domain registrars, social media and even gaming accounts (like Epic) are able to be set up with security keys.

Your first step is to find out what services are compatible. You can check directly on YubiKey’s website, but let’s use Twitter as an example.
You already secure your Twitter account with a login and password, but let’s say you want to add an extra layer of protection. Inside your Twitter account security settings is an area to activate 2FA, whether through text message, authenticator app or security key. I think you must activate 2FA through an authenticator app, first, like Google Authenticator, Microsoft Authenticator, or Authy. There are others, but you’re going to want to get one of these set up, first.
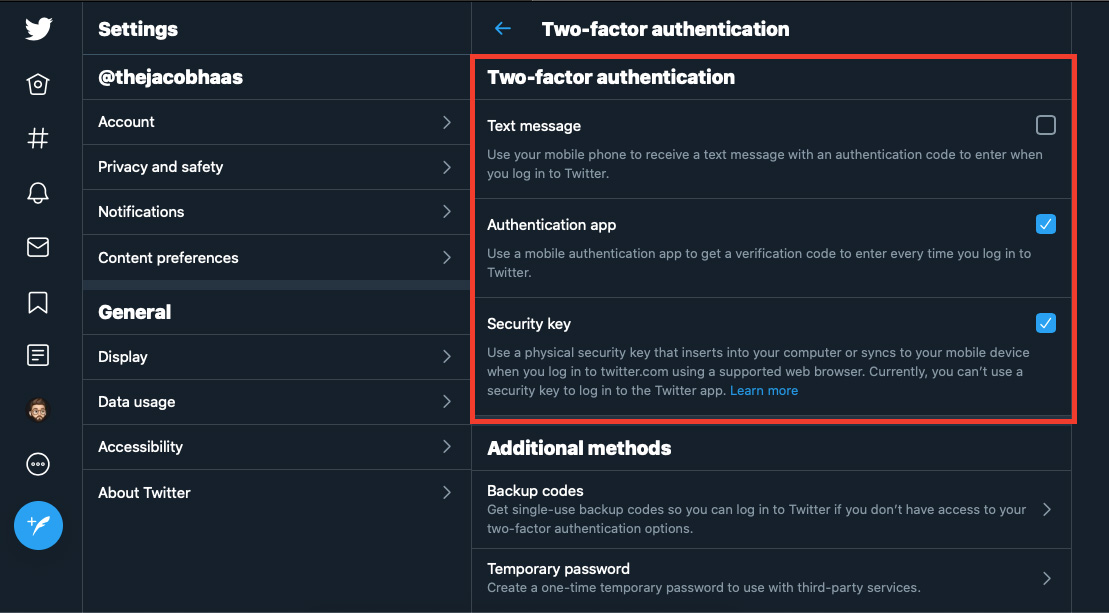
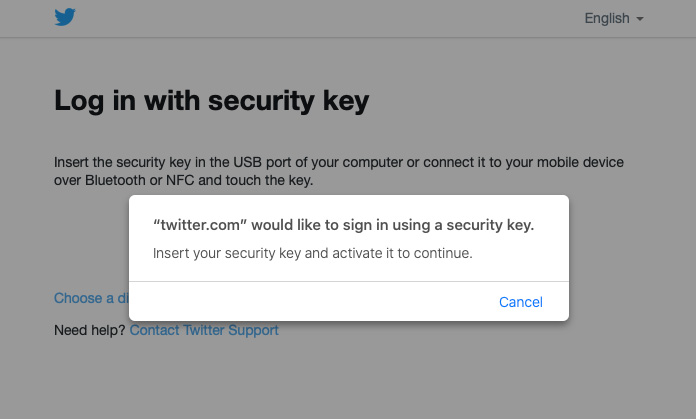
Once that’s done, you can choose to tie a YubiKey to your account. It will ask you to connect the key to your device, “activate” the key, which in the case of the 5Ci, pressing on the two small prongs on the side of the device. Once the key is paired to your account, you can choose to use it as your 2FA method.
Now, you must repeat this process with all of your other accounts. It’s … cumbersome, for sure. Depending on how many accounts you’d want to attach to the key, you could be looking at an afternoon of logging in, setting up 2FA, and tapping that key. But the good news is that once you do have those accounts set up, it’s a much quicker way of authentication.
Design and Performance
There’s not much to the YubiKey 5Ci, itself. It’s very small, very portable, and has a little hole in the middle of the key itself, perfect for adding to a keyring or small key hook.
The 5Ci has both USB-C and Lightning connectors, which is extremely useful and probably its most unique feature. It’s definitely forward-thinking of them, as most newer devices would accept at least one of these formats.
It’s a little awkward to put right on a keychain with a bunch of other keys. It doesn’t get in the way, per se, but it’s tricky to plug it into your phone or computer with a bunch of keys getting in the way. I haven’t figured out a good solution just yet, and have been instead carrying it in a small pocket in my bag.

Speaking of awkward, I very quickly realized just how few devices I have that natively accept USB-C. Newer MacBooks and iPad Pros have a USB-C port on them, but if you’re rocking something more than a couple years old, you’re pretty much stuck with needing an adapter. In fact, the first thing I had to do before I could try it out was grab a USB-C to USB-A adapter off Amazon for a few bucks, add it to the YubiKey, and pretty much leave it attached.
In use, and after attaching the key to all of my compatible accounts, the YubiKey was very simple to use. Just plug it in when prompted, activate it by touching both side prongs with your fingers (sort of completing the circuit) and the key works its magic. No typing in codes from text messages. No playing “beat the clock” with authenticators.
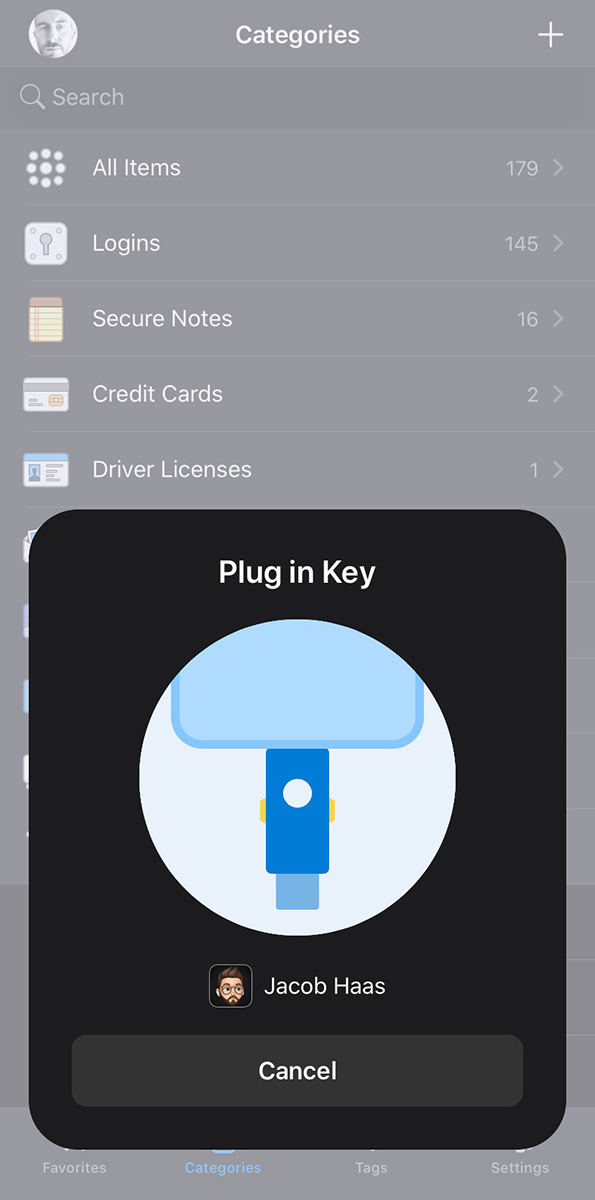
As of iOS 13.3, which made its way to the pubic only a few weeks ago, iPhones and iPads are now compatible with YubiKeys. I gave that a test as well when logging in to 1Password, my password cataloging app of choice, and it gave me a nice little graphical prompt to plug my key into the bottom of my phone, and worked perfectly.
I don’t think you’re able to actually set up a YubiKey on a mobile platform as of writing. I tried to do so in a couple instances in Mobile Safari and the browser didn’t seem to have that capability. I could be mistaken, but I think for now you’re going to need to use a desktop browser to set up the key with your accounts.
So by now you’re probably asking yourself, is it even worth grabbing a security key like this vs. using some other 2FA method? Your mileage may vary, for sure, but with massive data breaches happening in increasing frequency, I would for sure recommend you at least turn on 2FA on every account you possibly can. Even if someone were to get ahold of your login/password, you’d at least be the only one getting a text message with that 2FA code in it.
And once you start having to use that method often, you might get sick of seeing so many 2FA text messages cluttering up your Messages app, and find that plunking down a little bit of cash to set yourself up with a YubiKey is worth the initial setup for the extra security and ease of use.
What I like
- Very fast authentication
- Small and durable
- Offers peace of mind in protecting your online accounts
What I’d change
- A USB-C to USB adapter might have been nice
- Limited use in a mobile-only setting
- Shape is a little awkward on a keychain
Final thoughts
While a hardware security key might not be for everyone, it is a very quick alternative for 2FA. And I very much like the dual desktop/mobile function of the YubiKey 5Ci. Although it was a little awkward to use, personally, since I didn’t have any USB-C ports on my old MacBook.
Plus, now that iOS has been updated to take advantage of YubiKeys, there will likely be an increased acceptance of this technology on the application level.
Keep your eye on these devices, I’m certain they will become much more common as internet security is pushed to the front of the average user’s mind.
Price: $70
Where to buy: You can pick up a YubiKey 5Ci directly from their website.
Source: The sample of this product was provided by YubiCo.



Gadgeteer Comment Policy - Please read before commenting
So do you need to constantly attached the key to check your emails/facebook/etc on your phone? Or is this more of a first-time login thing when once the browser remembers you and doesn’t log you out that you stay logged in without having to use this key again?
Hi, Jackie, that’s a good question.
It’s the latter, like a first-time login. If you set your browser or app to recognize that computer or device going forward, it won’t ask for 2-factor authentication anymore.
Conversely, you can choose to not remember your credentials, like maybe you don’t want to save personal passwords on a work computer, and then would need that key each time you log in.
Thanks for the clarification. Always wanted to get into these keys but dread having to constantly plug them in every single time I need to visit a site.
As someone who’s had one for a while: Admittedly, it does somewhat depend on the site – some sites seem to require re-authenticating fairly often. Usually though it’s just a first-time login. (Or every 30 days, or something similar.)
They do have smaller models designed to be left in the USB port as well – but those aren’t really for your phone.
Thanks for the extra explanation up front, Jacob. That clarified things.
I would say the principle advantage of Fido keys is the protected afforded against phishing. You touched on phishing protection at the start of the article, but it is worth adding that Fido offers advanced protection against Man-in-the-middle style phishing attacks that are not present in most of the alternative authentication methods.
Hello!
Question…..
Does the Yubikey 5Ci require you to plug directly into your laptop or will it work with an external USB Splitter/USB hub?
Some computers have limited USB ports and a lot of times they are already in use…….
Thank you!