
REVIEW – In a previous YubiKey review, I mentioned how we now live in a world where many websites are being compromised. Along with mobile authenticator apps available, using a hardware device such as the YubiKey is great for extra login security. I had the opportunity to take a look at the newest of Yubico’s hardware keys; the YubiKey 5 NFC. Let’s take a look!
What is it?
The YubiKey 5 NFC is a hardware-based authentication device that provides extra authentication over NFC (Near Field Communications). It also supports FIDO2, allowing organizations to enable passwordless login on a computer that supports FIDO2 open authentication standards.
Hardware specs
- Dimensions: 0.7 in x 1.8 in x 0.13 in
- Weight: 0.04 oz
What’s in the box?
- YubiKey 5 NFC along with paper documentation
Design and features

The YubiKey 5 NFC looks much like any traditional USB device, but is flat and with a gold disk in the center of the key. It also has a keyhole to keep it on a lanyard with your EDC gear. I find it useful to keep in my backpack since I have it with me every day and keep it separate to my cell phone that I carry in my pocket.
Setup
Just like with the YubiKey 4 and other series, you can add this hardware key to tons of online services that support two-factor authentication. You can look into account preferences for an option along the lines of “set up a hardware key”. Then insert your YubiKey into your computer’s USB port, follow instructions, and all is set. When logging in, you touch the gold plating on the YubiKey to activate log on.

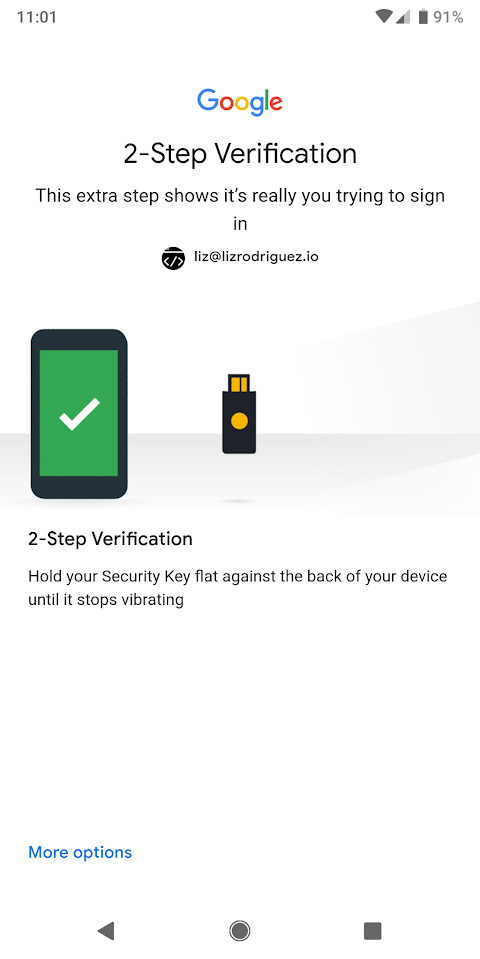
With this YubiKey 5 NFC, you can simply touch the key to the back of your phone (if your supports NFC). I have the Google Pixel 2 XL, and was able to set up my second Google account easily. I touched the key to the back of my phone shown above. It buzzed and then logged me in. It’s a little bit easier than using my mobile authenticator app, copying the password, and then logging into the site directly.
The software and services that support two-factor authentication with YubiKey are listed on their website. You can also use the YubiKey Authenticator for desktop or Android to generate OATH credentials on your YubiKey. Note: Since I already use the Authy Authenticator app with all my online services, I didn’t test this out. It’s also possible to log onto Windows 10 and all Microsoft accounts using the YubiKey. (Windows 10 version 1809 update and Microsoft Edge need to be installed for this to work.)
What I like
- Extra security for most online services such as Google, Dropbox, most social media sites etc.
- Durable, waterproof, and crush resistant
- Fits on a key chain for portability
What needs to be improved
- If you lose your YubiKey, then you’ll need to reconfigure all of your apps to use another authentication method
- Expensive for a small usb device
Final thoughts
Overall, as someone who appreciates an extra layer of security in her web apps, I really love using my YubiKey. It puts my mind a bit more at ease when logging onto my laptop, work machine, or phone. I think it’s very much worth grabbing one if you can!
Price: $45.00
Where to buy: You can purchase the YubiKey 5 NFC directly via their website or various online resellers including Amazon.
Source: The sample of this product was provided by Yubico.



Gadgeteer Comment Policy - Please read before commenting
If anyone is thinking of buying this, please keep in mind that Google requires two of these keys in case you lose one (only applies to your Google account). The keys are usually bundled together, like Google’s Titan Key for $50. Also, most sites like your bank, most social media sites only support SMS or an authenticator app as the second form of authentication.
As far as I understand the Authenticator on Desktop or Mobile is different than using something like Authy. Authy would be software only (app), that means something that compromises your phone would potentially get access to your 2FA codes. The Yubi app works with your key (hardware) + the app (software), that means on its own cannot access the codes. That is better than software alone as it must physically authenticated against the key using NFC. Same goes for the desktop app, the credentials authenticate against a connected key. No key connected, no codes, connect another key that was not the originally, again no codes on the app.
As for what Conor said and what you posted here in case you lose the Yubikey, in fact not only Google recommends two, everyone does. You should always have a minimum of 2 hardware keys exactly because of potential problems like lost, stolen, damaged, etc. When you authenticate against services, do it on both at the same time, leave one at home or in a safe place. That way you have a backup and one on the go or for daily use. Same is true for Google Authenticators or similar apps, if you are not using Authy (authy makes backup to a remote server…), you should copy or save the QR code or have at least 2 different phones (like a table and phone) for each service. Otherwise if you lose the phone or reset it you have the same issue and are locked out of your services. The 2 per person applies to all 2FA devices.
Now, as with everything in terms of security, more extra steps means more security but more hassle while using and logging into services. As for the Windows authentication, there is a flaw and people complain about this. The YubiKey lets you log in automatically into Windows but it seems it cannot work as a second authentication method. It’s either the Yubikey or nothing. That is not what some people would call more secure than just a password. Same for password less logins that use FIDO. While not having to log with a password might seem a great idea at first, it’s a nightmare if you ever lose the key or someone gets access to your YubiKey, now the YubiKey is the key to whole kingdom….
My advise? Don’t ever use a device like this as the only authentication method. Use it as a 2FA device, in combination with another login method, that means plus a password or something else. While Yubikey being hardware based prevents software/remote hacks, it’s very dangerous if its gets stolen or lost, hence you should always use it together with a password but never alone.
I’d be more interested in the difference between the Yubikey 5 Series and the Yubikey Security Key Series sold for half the price. I can’t figure it out from the Yubico website.
Simple!
The YK5 Family supports: PGP, PIV smart card, OATH-TOTP (time based OTPs), OATH HOTP (event based OTPs), YubiOTP, U2F and FIDO2. And you can store secrets on the key needed for Challenge Response base auth. as well as “static credentials”.
The Security Key supports ONLY U2F and FIDO2.
The Yubikey 5 Series is compatible with more services, particularly the more secure U2F and FIDO2 protocols. It also supports one-time passwords (OTP) and will work with Lastpass which only supports OTP security keys, among other less secure 2FA methods.
The Yubikey security key does NOT support OTP so it won’t work with Lastpass or any website that uses OTP. This was the main reason I dumped Lastpass and moved to a more secure password manager that supports U2F.
Hello! Please tell me where you can buy these two keys so that they really work as they should. Thanks in advance for the information!
Question: Your review was more helpful than Yubico’s site, but are you using the key to log into the phone, just certain apps, or both?
Also, same question as Steve: what is the Security key about? Yubico says almost nothing.
The big difference is the extra protocols and security types the 5 Series supports.
Both support
U2F, and FIDO2
Which will give you access to most of the dual factor Auth systems out there
The N Series is more for high level security people, or programers, who need the ability to support the more uncommon protocols
OATH – HOTP, and TOTP
SmartCard emulation
OpenPGP Hardware encryption/decryption
RSA 4k PGP keys
RSA 2k Standard Keys
My Job requires I have access to OpenPGP keys for our code repositories. So I need this support myself.
However I personally prefer the “OnlyKey” which is similar, but supports an unlock/destroy key code to be physically entered on the device before it’s unlocked. It also supports up to 2 separate profiles, each with 12 identities. So in theory it can replace 24 separate yubi keys. The OnlyKey has a little steeper learning curve, and lacks NFC. I keep an USB C adaptor on mine, so I just plug it into my phone and tablet when I need it. Between work and personal I would need 6 separate YubiKeys, so I find this a much better solution.
https://onlykey.io/
Note: I highly recommend everybody use both a hardware key and password manager, to ensure you use separate passwords for every site you visit. I use an OnlyKey and LastPass myself. They work great together. But LastPass works just as well with YubiKey. Most of the other well known password managers also support both hardware keys.
The key is practical (if a bit expensive) but it should be noted that whilst browser support has improved hugely, website support outside of the social media sites is still thin on the ground.
Hello! Please tell me where you can buy these two keys so that they really work as they should. Thanks in advance for the information!